Does a private messenger have to know the phone number of communicating parties?
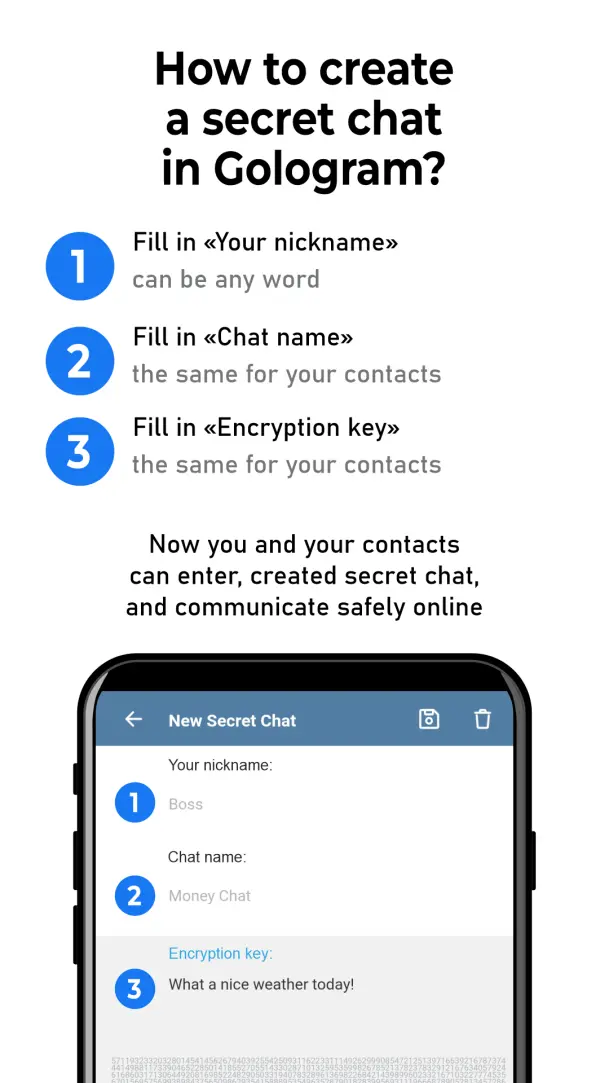
Gologram does not have access to your contacts, it doesn’t know your phone number or the numbers of others. Gologram is a truly private messenger.
The phone numbers of the communication parties and contact are unknown.
No need to register it.
No access to camera, calendar, location, fingerprints, microphone, contacts, or phone number.
Encrypted messages are sent directly online without a server and no logs.
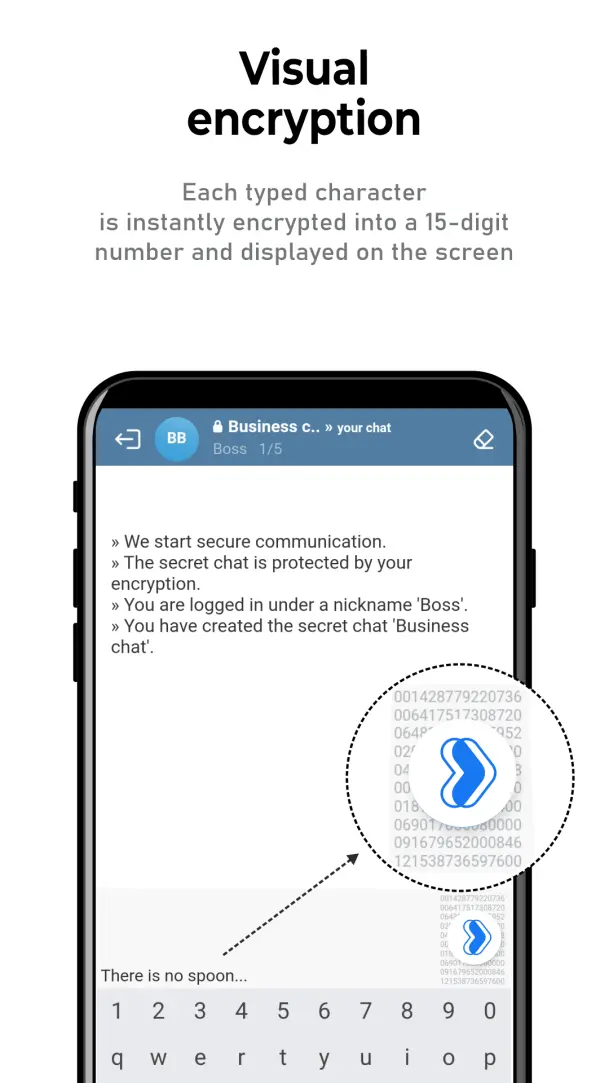
Each typed character is instantly encrypted into a 15-digit number and displayed on the screen.
No one can imperceptibly disable end-to-end encryption for you.
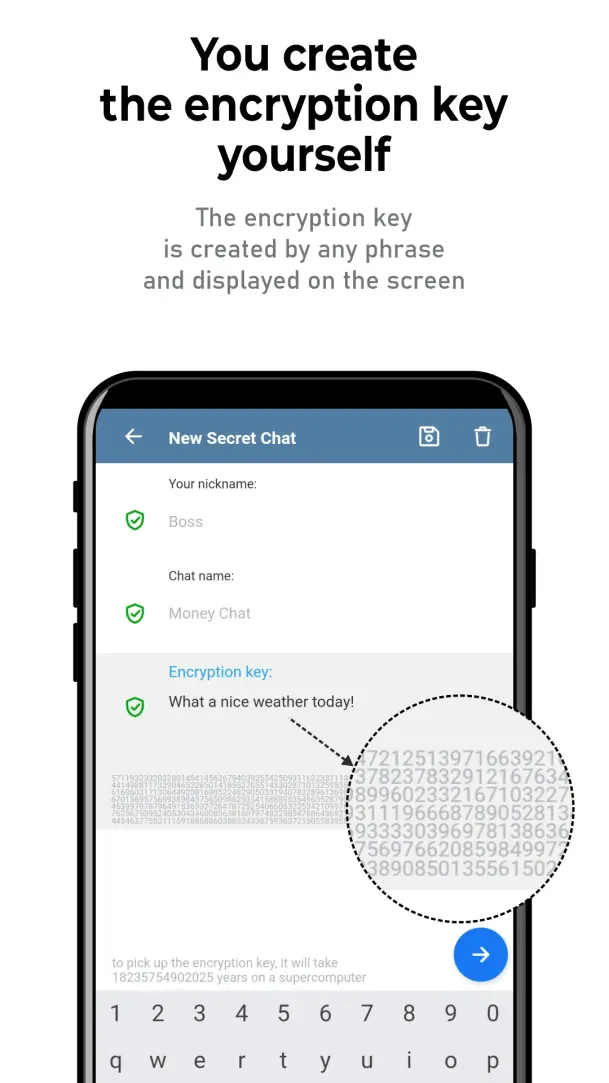
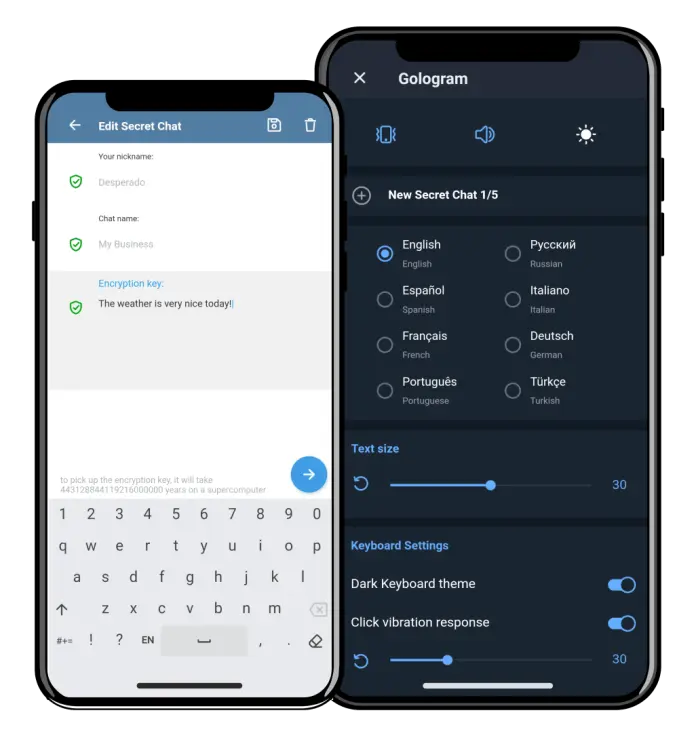
You invent and create an encrypted key yourself using any phrase which’ll be instantly displayed on the screen.
Communication done directly online only without a use of a server or a cloud.
There is no exchange of encryption keys, there is no sending of encryption keys to the server.
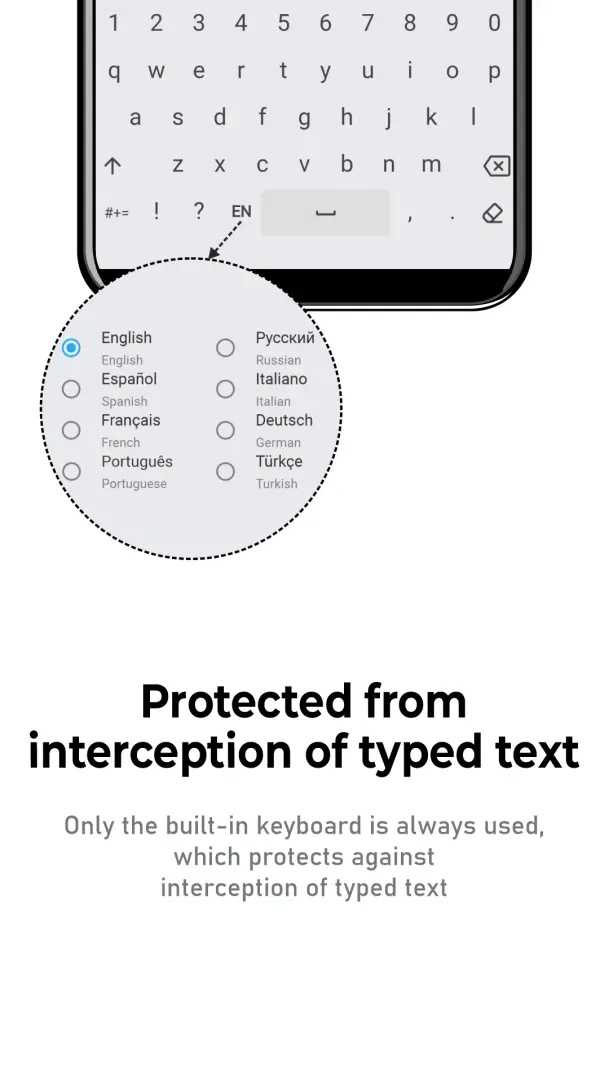
The built-in keyboard protects against interception of the typed message.
The only thing is going to be sent is the encrypted text of 15 digit numbers that was displayed on the screen.
Do you think it’s safe when the messenger creates an encryption key for you and stores it on the server with your messages?
In Gologram you create an encryption key yourself, and it’s stored on your device only. Gologram is a really secure messenger.